This Book is Out of Stock!
English
Paperback
₹3418
₹3599
5.03% OFF
(All inclusive*)
Delivery Options
*COD & Shipping Charges may apply on certain items.
Review final details at checkout.
Looking to place a bulk order? SUBMIT DETAILS
About The Book
Description
Author
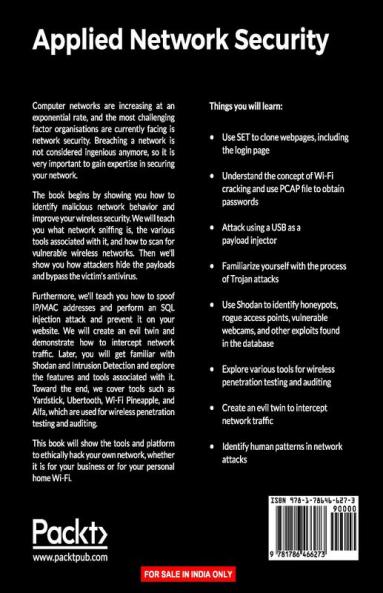
Master the art of detecting and averting advanced network security attacks and techniques About This Book. Deep dive into the advanced network security attacks and techniques by leveraging tools such as Kali Linux 2 MetaSploit Nmap and Wireshark. Become an expert in cracking WiFi passwords penetrating anti-virus networks sniffing the network and USB hacks. This step-by-step guide shows you how to confidently and quickly detect vulnerabilities for your network before the hacker does Who This Book Is For This book is for network security professionals cyber security professionals and Pentesters who are well versed with fundamentals of network security and now want to master it. So whether youre a cyber security professional hobbyist business manager or student aspiring to becoming an ethical hacker or just want to learn more about the cyber security aspect of the IT industry then this book is definitely for you. What You Will Learn. Use SET to clone webpages including the login page. Understand the concept of Wi-Fi cracking and use PCAP file to obtain passwords. Attack using a USB as payload injector. Familiarize yourself with the process of trojan attacks. Use Shodan to identify honeypots rogue access points vulnerable webcams and other exploits found in the database. Explore various tools for wireless penetration testing and auditing. Create an evil twin to intercept network traffic. Identify human patterns in networks attacks In Detail Computer networks are increasing at an exponential rate and the most challenging factor organisations are currently facing is network security. Breaching a network is not considered an ingenious effort anymore so it is very important to gain expertise in securing your network. The book begins by showing you how to identify malicious network behaviour and improve your wireless security. We will teach you what network sniffing is the various tools associated with it and how to scan for vulnerable wireless networks. Then well show you how attackers hide the payloads and bypass the victims antivirus. Furthermore well teach you how to spoof IP / MAC address and perform an SQL injection attack and prevent it on your website. We will create an evil twin and demonstrate how to intercept network traffic. Later you will get familiar with Shodan and Intrusion Detection and will explore the features and tools associated with it. Toward the end we cover tools such as Yardstick Ubertooth Wifi Pineapple and Alfa used for wireless penetration testing and auditing. This book will show the tools and platform to ethically hack your own network whether it is for your business or for your personal home Wi-Fi. Style and approach This mastering-level guide is for all the security professionals who are eagerly waiting to master network security skills and protecting their organization with ease. It contains practical scenarios on various network security attacks and will teach you how to avert these attacks. About the Author Arthur Salmon is a lead security professional for Rex Technology Services Las Vegas NV. He is the program director of a community college for their cyber security program. Arthur currently holds a masters degree in network and communication management focusing on security. He is also finishing up his dissertation for a PhD in information security assurance. He has over 80 IT certifications including his VMware VCP Cisco CCNP:RnS/CCDP and numerous CCNAs (RnS security design voice and video collaborations to name a few). He also holds other certifications from vendors such as Microsoft CompTIA Juniper Six Sigma EMC ISC2 Encase and so on. Currently hes awaiting results for his exams for ISC2 CISSP CEH and forensic investigator. He has worked in the IT sector for over 15 years. He is currently working on writing and collaborating new books articles or any other learning material. Warun Levesque has worked for various technical companies and projects over the past five years in information technology and network security. He began his academic path back in 2011 where his focus centered around mobile application development and web application programming. During this time he worked on the development of many guides and educational resources contributing to the cyber security community. Warun has also accepted various contracts including one from a major IT Corporation to provide technical support and guidance to set up network and assistance for businesses nationwide. For the past couple of years he has taken the role of a consultant for various companies including institutional support for cyber security related training and classes. He is also the cofounder of a community of ethical hackers where he continues to learn and develop both his skills and effective guides for offensive defensive and mitigation in cyber security. Michael McLafferty has been researching on cyber security and applied ethical hacking for over 6 years. His interest in cyber security started in 2010. At the time he was creating search engine optimization scripts for various small businesses. His clients would also ask him to secure their websites which led him to find his passion in cyber security instead of search engine optimization. In 2012 he became a private cyber security consultant for both individuals and small businesses. He would provide network and endpoint security advice as well as social engineering awareness training to employees and individuals. He is also a paid cyber security researcher sponsored by local businesses to further the advancement of cyber security methods and applied knowledge. He is the co-founder of an open society of ethical hackers that meets weekly to discuss and apply new cyber security skills. They have full access to both a lab and cutting-edge ethical hacking equipment to develop new methods in offensive security. He is also an inventor. He and his business partner have patents pending on various cyber security tools and software. They continue with their research with great passion and drive. He is committed to reshaping and setting new standards in the world of cyber security. With the level of collaboration from his colleagues he firmly believes that they can achieve this.
*COD & Shipping Charges may apply on certain items.
Review final details at checkout.
₹3418
₹3599
5% OFF
Paperback
Out Of Stock
All inclusive*
Details
ISBN 13
9781786466273
Publication Date
-28-04-2017
Pages
-350
Weight
-610 grams
Dimensions
-190.5x234.95x18.58 mm