English
Paperback
₹786
₹849
7.42% OFF
(All inclusive*)
Delivery Options
Please enter pincode to check delivery time.
*COD & Shipping Charges may apply on certain items.
Review final details at checkout.
Looking to place a bulk order? SUBMIT DETAILS
About The Book
Description
Author
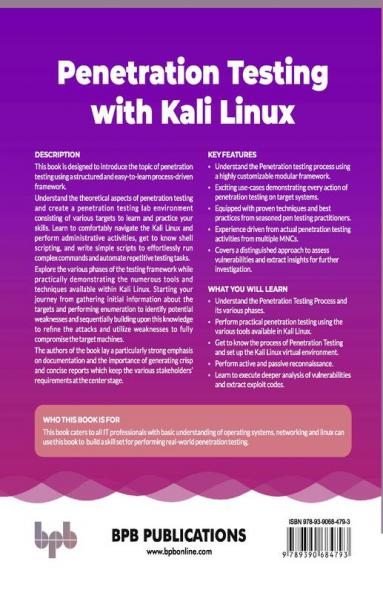
Perform effective and efficient penetration testing in an enterprise scenario Key Features● Understand the penetration testing process using a highly customizable modular framework.● Exciting use-cases demonstrating every action of penetration testing on target systems.● Equipped with proven techniques and best practices from seasoned pen-testing practitioners.● Experience-driven from actual penetration testing activities from multiple MNCs. DescriptionThis book is designed to introduce the topic of penetration testing using a structured and easy-to-learn process-driven framework. Understand the theoretical aspects of penetration testing and create a penetration testing lab environment consisting of various targets to learn and practice your skills. Learn to comfortably navigate the Kali Linux and perform administrative activities get to know shell scripting and write simple scripts to effortlessly run complex commands and automate repetitive testing tasks. Explore the various phases of the testing framework while practically demonstrating the numerous tools and techniques available within Kali Linux. Starting your journey from gathering initial information about the targets and performing enumeration to identify potential weaknesses and sequentially building upon this knowledge to refine the attacks and utilize weaknesses to fully compromise the target machines. The authors of the book lay a particularly strong emphasis on documentation and the importance of generating crisp and concise reports which keep the various stakeholders requirements at the center stage. What you will learn● Understand the Penetration Testing Process and its various phases.● Perform practical penetration testing using the various tools available in Kali Linux.● Get to know the process of Penetration Testing and set up the Kali Linux virtual environment. Who this book is forThis book caters to all IT professionals with a basic understanding of operating systems networking and Linux can use this book to build a skill set for performing real-world penetration testing. Table of Contents1. The Basics of Penetration Testing2. Penetration Testing Lab3. Finding Your Way Around Kali Linux4. Understanding the PT Process and Stages5. Planning and Reconnaissance6. Service Enumeration and Scanning7. Vulnerability Research8. Exploitation9. Post Exploitation10. Reporting About the Authors Pranav Joshi has over 20 years of Information and Cybersecurity experience in leading and delivering large-scale projects for clients in diverse business verticals such as banking finance national stock exchanges insurance energy petrochemical retail media advertising e-commerce IT & ITES government defense including Fortune 100 companies. In his previous role he has been responsible for managing the security of information assets infrastructure and applications covering 65 countries significantly reducing compliance-related incidents. LinkedIn Profile: https: // Deepayan Chanda a seasoned cybersecurity professional architect cybersecurity strategist and advisor has a strong intent to solve cybersecurity problems for enterprises. He is driven by more than 24 years of diverse security domain experience and creates a balance between security and business goals. He has worked for the Indian Air Force. Currently he is working with National Australia Bank. LinkedIn Profile: https: //
Delivery Options
Please enter pincode to check delivery time.
*COD & Shipping Charges may apply on certain items.
Review final details at checkout.
Details
ISBN 13
9789390684793
Publication Date
-31-07-2021
Pages
-278
Weight
-489 grams
Dimensions
-190.5x234.95x14.88 mm