English
Paperback
₹917
₹999
8.21% OFF
(All inclusive*)
Delivery Options
Please enter pincode to check delivery time.
*COD & Shipping Charges may apply on certain items.
Review final details at checkout.
Looking to place a bulk order? SUBMIT DETAILS
About The Book
Description
Author
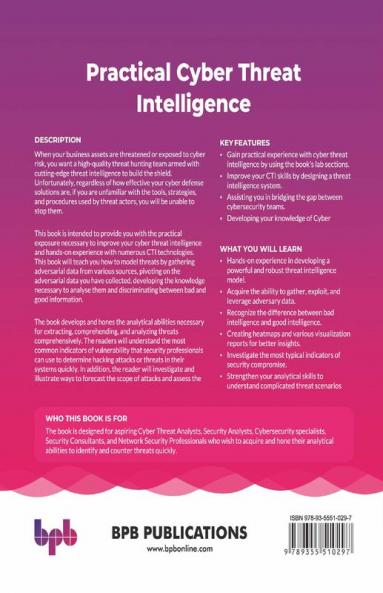
Knowing your threat actors together with your weaknesses and the technology will master your defenseKEY FEATURES ● Gain practical experience with cyber threat intelligence by using the books lab sections.● Improve your CTI skills by designing a threat intelligence system.● Assisting you in bridging the gap between cybersecurity teams.● Developing your knowledge of Cyber Intelligence tools and how to choose them.DESCRIPTION When your business assets are threatened or exposed to cyber risk you want a high-quality threat hunting team armed with cutting-edge threat intelligence to build the shield. Unfortunately regardless of how effective your cyber defense solutions are if you are unfamiliar with the tools strategies and procedures used by threat actors you will be unable to stop them.This book is intended to provide you with the practical exposure necessary to improve your cyber threat intelligence and hands-on experience with numerous CTI technologies. This book will teach you how to model threats by gathering adversarial data from various sources pivoting on the adversarial data you have collected developing the knowledge necessary to analyse them and discriminating between bad and good information.The book develops and hones the analytical abilities necessary for extracting comprehending and analyzing threats comprehensively. The readers will understand the most common indicators of vulnerability that security professionals can use to determine hacking attacks or threats in their systems quickly.WHAT YOU WILL LEARN● Hands-on experience in developing a powerful and robust threat intelligence model.● Acquire the ability to gather exploit and leverage adversary data.● Recognize the difference between bad intelligence and good intelligence.● Creating heatmaps and various visualization reports for better insights.● Investigate the most typical indicators of security compromise.WHO THIS BOOK IS FORThe book is designed for aspiring Cyber Threat Analysts Security Analysts Cybersecurity specialists Security Consultants and Network Security Professionals who wish to acquire and hone their analytical abilities to identify and counter threats quickly.
Delivery Options
Please enter pincode to check delivery time.
*COD & Shipping Charges may apply on certain items.
Review final details at checkout.
Details
ISBN 13
9789355510297
Publication Date
-27-05-2022
Pages
-452
Weight
-777 grams
Dimensions
-190x234x23.82 mm